Abstract
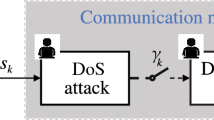
In this paper, we investigate the defense problem against the joint attacks of denial-of-service attacks and data tampering attacks in the framework of system identification with binary-valued observations. By estimating the key parameters of the joint attack and compensating them in the identification algorithm, a compensation-oriented defense scheme is proposed. Then the identification algorithm of system parameter is designed and is further proved to be consistent. The asymptotic normality of the algorithm is obtained, and on this basis, we propose the optimal defense scheme. Furthermore, the implementation of the optimal defense scheme is discussed. Finally, a simulation example is presented to verify the effectiveness of the main results.










Similar content being viewed by others
References
Zhang, Y., Qiu, M., Tsai, C. W., Hassan, M. M., & Alamri, A. (2017). Health-CPS: Healthcare cyber-physical system assisted by cloud and big data. IEEE Systems Journal, 11(1), 88–95.
Lv, C., Hu, X., Sangiovanni-Vincentelli, A., Li, Y., Martinez, C. M., & Cao, D. (2019). Driving-style-based codesign optimization of an automated electric vehicle: A cyber-physical system approach. IEEE Transactions on Industrial Electronics, 66(4), 2965–2975.
Cintuglu, M. H., Mohammed, O. A., Akkaya, K., & Uluagac, A. S. (2017). A survey on smart grid cyber-physical system testbeds. IEEE Communications Surveys & Tutorials, 19(1), 446–464.
Karnouskos, S. (2011). Stuxnet worm impact on industrial cyber-physical system security. In the 37th Annual Conference of the IEEE Industrial Electronics Society (pp. 4490–4494), Melbourne, Australia.
Wang, E. K., Ye, Y., Xu, X., Yiu, S. M., Hui, L. C. K., & Chow, K. P. (2010). Security issues and challenges for cyber physical system. In IEEE/ACM Int’l Conference on Green Computing and Communications & Int’l Conference on Cyber, Physical and Social Computing (pp. 733–738), Washington, DC, USA.
Gao, Y., Wang, L., Ren, W., Xie, F., Mo, X., Luo, X., et al. (2020). Reinforcement learning-based detection method for malware behavior in industrial control systems. Chinese Journal of Engineering, 42(4), 455–462.
Chen, J., Huang, B., Ding, F., & Gu, Y. (2018). Variational Bayesian approach for ARX systems with missing observations and varying time-delays. Automatica, 94, 194–204.
Cao, H. Y., Zhu, P. D., Lu, X. C., & Gurtov, A. (2013). A layered encryption mechanism for networked critical infrastructures. IEEE Network, 27(1), 12–18.
Saxena, N., & Grijalva, S. (2018). Efficient signature scheme for delivering authentic control commands in the smart grid. IEEE Transactions on Smart Grid, 9(5), 4323–4334.
Kumar, P., Braeken, A., Gurtov, A., Iinatti, J., & Ha, P. H. (2017). Anonymous secure framework in connected smart home environments. IEEE Transactions on Information Forensics and Security, 12(4), 968–979.
Zhang, Y. C., Wang, L. F., Sun, W. Q., Green, R. C., II., & Alam, M. (2011). Distributed intrusion detection system in a multi-layer network architecture of smart grids. IEEE Transactions on Smart Grid, 2(4), 796–808.
Shi, D., Guo, Z., Johansson, K. H., & Shi, L. (2018). Causality countermeasures for anomaly detection in cyber-physical systems. IEEE Transactions on Automatic Control, 63(2), 386–401.
Qi, S., Zhang, K. W., & Shi, Y. (2020). Resilient model predictive control of cyber-physical systems under DoS attacks. IEEE Transactions on Industrial Informatics, 16(7), 4920–4927.
Lai, S. Y., Chen, B., Li, T. X., & Yu, L. (2019). Packet-based state feedback control under DoS attacks in cyber-physical systems. IEEE Transactions on Circuits and Systems II: Express Briefs, 66(8), 1421–1425.
Xu, Y., Fang, M., Wu, Z., Pan, Y., Chadli, M., & Huang, T. (2020). Input-based event-triggering consensus of multiagent systems under denial-of-service attacks. IEEE Transactions on Systems, Man, and Cybernetics: Systems, 50(4), 1455–1464.
Yu, L., Sun, X., & Sui, T. (2019). False-data injection attack in electricity generation system subject to actuator saturation: Analysis and design. IEEE Transactions on Systems, Man, and Cybernetics: Systems, 49(8), 1712–1719.
Yang, Q., Yang, J., Yu, W., An, D., Zhang, N., & Zhao, W. (2014). On false data-injection attacks against power system state estimation: Modeling and countermeasures. IEEE Transactions on Parallel and Distributed Systems, 25(3), 717–729.
Miao, F., Pajic, M., & Pappas, G. J. (2013). Stochastic game approach for replay attack detection. In the 52nd IEEE Conference on Decision and Control (pp. 1854–1859), Florence, Italy.
Guo, J., Diao, J. D. (2020). Prediction-based event-triggered identification of quantized input FIR systems with quantized output observations. Science China Information Sciences, 63, 112201:1–112201:12.
Diao, J. D., Guo, J., & Sun, C. Y. (2018). Event-triggered identification of FIR systems with binary-valued output observations. Automatica, 98, 95–102.
Tan, S., Guo, J., Zhao, Y., & Zhang, J. F. (2021). Adaptive control with saturation-constrainted observations for drag-free satellites—a set-valued identification approach. Science China Information Sciences. https://doi.org/10.1007/s11432-020-3145-0.
Wang, L. Y., Yin, G. G., Zhang, J. F., & Zhao, Y. L. (2010). System Identification with Quantized Observations. Boston, MA: Birkhäuser.
Guo, J., Wang, L. Y., Yin, G. G., Zhao, Y. L., & Zhang, J. F. (2010). Asymptotically efficient identification of FIR systems with quantized observations and general quantized inputs. Automatica, 57, 113–122.
Athreya, K. B., & Lahiri, S. N. (2006). Measure Theory and Probability Theory. New York: Springer.
Chow, Y., & Teicher, H. (1997). Probability Theory: Independence, Interchangeability, Martingales. New York: Springer.
Guo, J., Wang, X. B., Xue, W. C., & Zhao, Y. L. (2020). System identification with binary-valued observations under data tampering attacks. IEEE Transactions on Automatic Control. https://doi.org/10.1109/TAC.2020.3029325
Muresan, M. (2009). A Concrete Approach to Classical Analysis. New York: Springer.
Acknowledgements
This research was supported by the National Key Research and Development Program of China (2018YFA0703801), the National Natural Science Foundation of China (62173030, 62033010).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Guo, J., Wang, X., Zhang, Y. et al. System identification with binary-valued observations under both denial-of-service attacks and data tampering attacks: defense scheme and its optimality. Control Theory Technol. 20, 114–126 (2022). https://doi.org/10.1007/s11768-021-00074-8
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11768-021-00074-8